|
|
|||||||||||||||
|
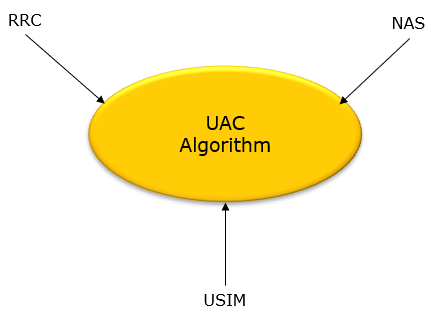
UAC is a set of mechanism (algorithm) to determine whether to allow the UE for a specific services or state changes. UAC is a pretty complicated algorithm that get many factors involved at each point of decision making process. Overall concept similar to LTE Access Control, but I think the related parameters are more dispersed here and there... causing more confusion -:). In LTE, Access control is mainy controlled by RRC(SIBs) but it seems NAS has more control ever Access Control in NR seems.
Factors for UAC mechanismThe rough categories of factors affecting UAC is illustarated below and main framework is specified in 24.501-4.5, but you may refer to additional specification like 38.331 and USIM specification for further details.
Triggers for Checking UACTriggers for UAC check is specified in 24.501-4.5.1 and can be summarized as follows.
RRC Information for UACSIB1 ::= SEQUENCE { cellSelectionInfo SEQUENCE { q-RxLevMin Q-RxLevMin, q-RxLevMinOffset INTEGER (1..8) OPTIONAL, -- Need R q-RxLevMinSUL Q-RxLevMin OPTIONAL, -- Need R q-QualMin Q-QualMin OPTIONAL, -- Need R q-QualMinOffset INTEGER (1..8) OPTIONAL -- Need R } OPTIONAL, -- Need S cellAccessRelatedInfo CellAccessRelatedInfo, connEstFailureControl ConnEstFailureControl OPTIONAL, -- Need R si-SchedulingInfo SI-SchedulingInfo OPTIONAL, -- Need R servingCellConfigCommon ServingCellConfigCommonSIB OPTIONAL, -- Need R ims-EmergencySupport ENUMERATED {true} OPTIONAL, -- Need R eCallOverIMS-Support ENUMERATED {true} OPTIONAL, -- Cond Absent ue-TimersAndConstants UE-TimersAndConstants OPTIONAL, -- Need R
uac-BarringInfo SEQUENCE { uac-BarringForCommon UAC-BarringPerCatList OPTIONAL, -- Need S uac-BarringPerPLMN-List UAC-BarringPerPLMN-List OPTIONAL, -- Need S uac-BarringInfoSetList UAC-BarringInfoSetList, uac-AccessCategory1-SelectionAssistanceInfo CHOICE { plmnCommon UAC-AccessCategory1-SelectionAssistanceInfo, individualPLMNList SEQUENCE (SIZE (2..maxPLMN)) OF UAC-AccessCategory1-SelectionAssistanceInfo } OPTIONAL } OPTIONAL, -- Need R
useFullResumeID ENUMERATED {true} OPTIONAL, -- Need N lateNonCriticalExtension OCTET STRING OPTIONAL, nonCriticalExtension SEQUENCE{} OPTIONAL }
UAC-AccessCategory1-SelectionAssistanceInfo ::= ENUMERATED {a, b, c}
UAC-BarringInfoSetList ::= SEQUENCE (SIZE(1..maxBarringInfoSet)) OF UAC-BarringInfoSet
UAC-BarringInfoSet ::= SEQUENCE { uac-BarringFactor ENUMERATED {p00, p05, p10, p15, p20, p25, p30, p40, p50, p60, p70, p75, p80, p85, p90, p95}, uac-BarringTime ENUMERATED {s4, s8, s16, s32, s64, s128, s256, s512}, uac-BarringForAccessIdentity BIT STRING (SIZE(7)) }
RRCSetupRequest ::= SEQUENCE { rrcSetupRequest RRCSetupRequest-IEs } RRCSetupRequest-IEs ::= SEQUENCE { ue-Identity InitialUE-Identity, establishmentCause EstablishmentCause, spare BIT STRING (SIZE (1)) }
InitialUE-Identity ::= CHOICE { ng-5G-S-TMSI-Part1 BIT STRING (SIZE (39)), randomValue BIT STRING (SIZE (39)) }
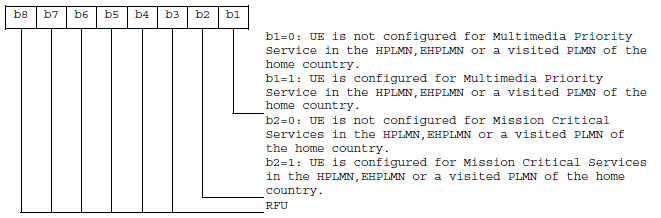
EstablishmentCause ::= ENUMERATED { emergency, highPriorityAccess, mt-Access, mo-Signalling, mo-Data, mo-VoiceCall, mo-VideoCall, mo-SMS, mps-PriorityAccess, mcs-PriorityAccess, spare6, spare5, spare4, spare3, spare2, spare1} USIM Information for UACEFUAC_AIC (UAC Access Identities Configuration) : 31.102-4.4.11.7
EFUAC_ACC (Access Control Class) : 31.102-4.2.15
How to determine Access Identity ?Basically Access Identity is determined by a few parameters in UICC as described in the following table. < 24.501-Table 4.5.2.1: Access identities >
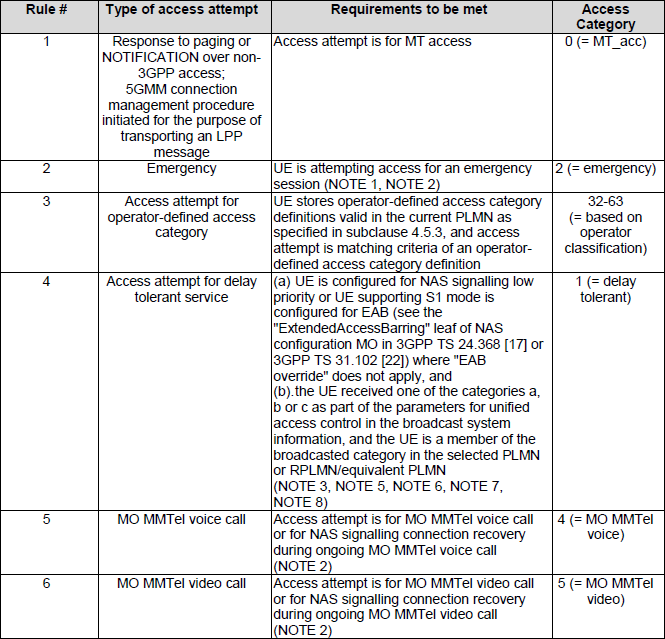
What kind of service can be provided for a access category ?< 24.501-Table 4.5.2.2: Mapping table for access categories >
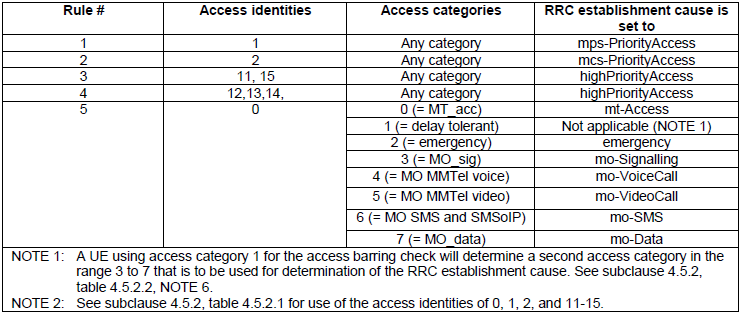
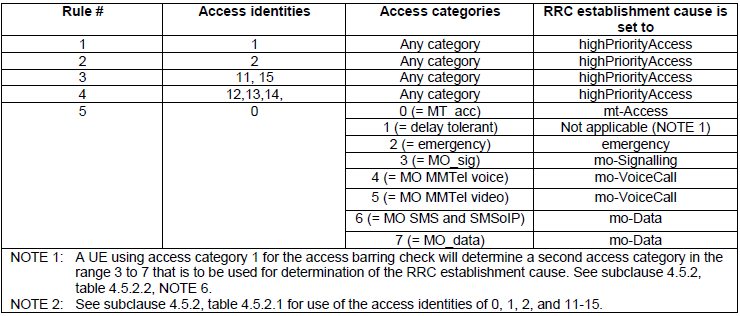
Mapping between access categories/access identities and RRC establishment cause< 24.501 - Table 4.5.6.1: Mapping table for access identities/access categories and RRC establishment cause when establishing N1 NAS signalling connection via NR connected to 5GCN >
< 24.501 - Table 4.5.6.2: Mapping table for access identities/access categories and RRC establishment cause when establishing N1 NAS signalling connection via E-UTRA connected to 5GCN >
Reference
|
|||||||||||||||